How the Job Application Fraud Scam Works
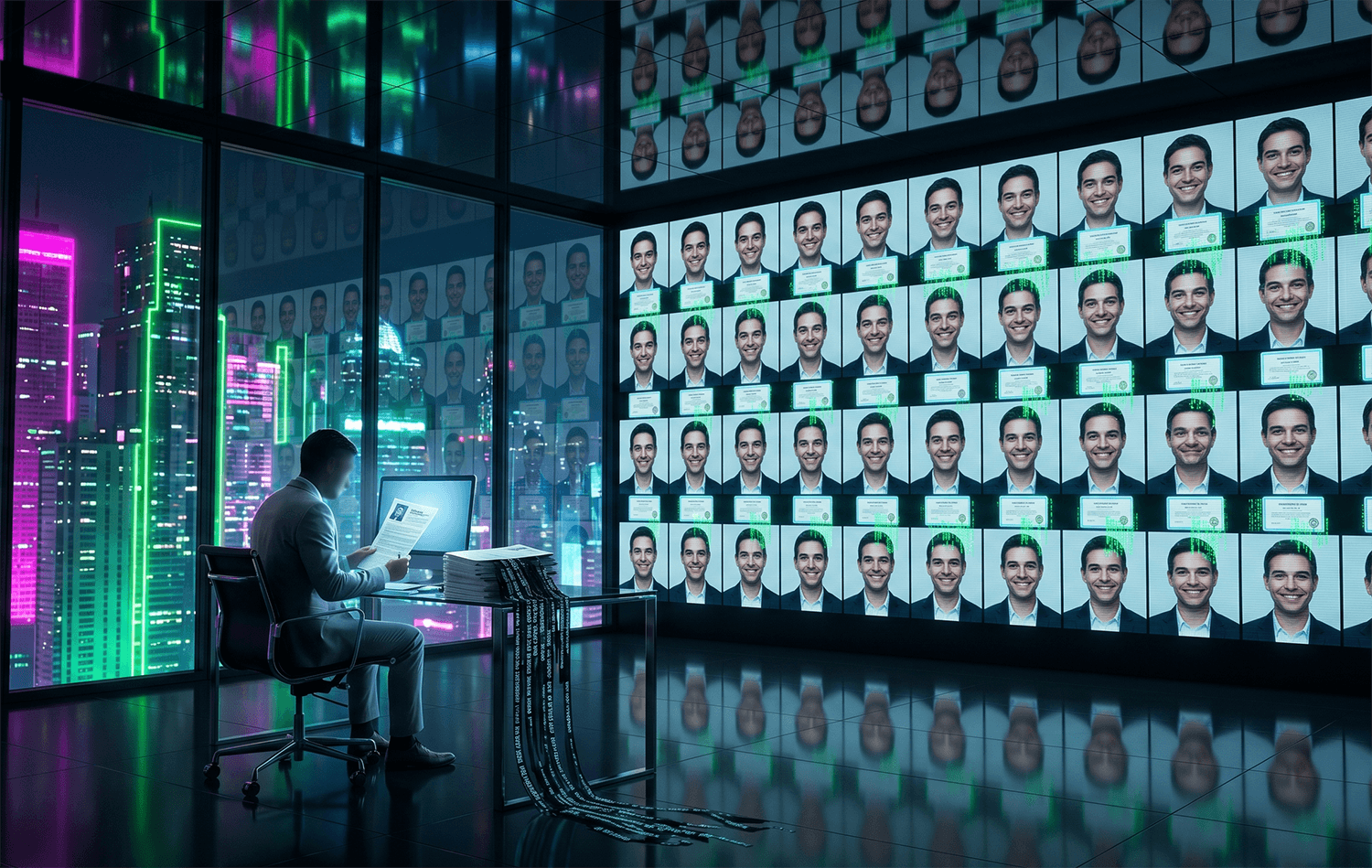
Criminals targeting your hiring process typically begin by researching your company's open positions, leadership structure, and recent job postings. They create fake LinkedIn profiles, resume documents, and email addresses that closely mimic legitimate candidate information. In many cases, scammers use stolen photos from social media or AI-generated profile images to build credibility. When they apply, their resumes are tailored to match your job description perfectly, often listing experience at well-known companies with dates and skills that seem almost too good to be true.
Once an application is submitted and catches an HR professional's attention, the scammer moves into the verification phase. They respond quickly to interview requests and may use video conferencing tools with intentionally poor connection quality to hide their identity or use deepfake technology to appear as someone else. Some criminals request an upfront payment for background checks, work-from-home setup fees, or certification verification before they can start. Others use the interview process to gather sensitive company information, client lists, or financial details that can be sold to competitors or used in subsequent scams targeting the company.
More sophisticated fraud rings operate by sending infected documents, requesting W-4 or I-9 forms early to steal personal identification details, or asking to be added to payroll before actually starting work. Once added to the payroll system, they may redirect direct deposit information, change banking details for other employees, or access internal systems to steal company data. In some cases, multiple fake candidates are hired simultaneously across different departments, allowing the criminal network to execute coordinated data theft or financial fraud targeting the entire organization.
The financial impact extends beyond direct losses. Companies may spend thousands in HR time conducting interviews, running background checks, and onboarding fake employees who never show up. Worse, if sensitive data is compromised, your company faces potential regulatory fines, reputational damage, and lawsuits from clients whose information was exposed.
Red Flags to Watch For
The resume is suspiciously perfect: every skill matches the job description exactly, employment dates have no gaps, and the candidate appears overqualified yet still interested in your entry-level position. This combination is extremely rare and suggests the resume was generated specifically to trick your screening process.
The candidate responds to interview invitations within minutes at unusual hours, showing an intensity that feels forced or scripted rather than naturally enthusiastic.
Video interview connections consistently experience technical issues: frozen screens, pixelated video, or audio dropout that conveniently prevents clear identification or causes the interview to be rescheduled.
The applicant requests an upfront payment for background checks, visa sponsorship fees, equipment, or training before employment begins. Legitimate employers cover these costs.
Email addresses are newly created accounts (checked via the domain registration date), or the candidate provides a personal email rather than a professional one, especially when claiming to work at major corporations.
LinkedIn profile shows recent activity only (created within weeks of applying), has few connections from verifiable sources, or uses a stock photo or slightly modified image that matches other fake profiles online.
The candidate asks unusual questions about payroll processing, banking information for direct deposit, access to company systems, or organizational structure before being hired or completing standard onboarding.
References provided are phone numbers without voicemail or email addresses, always reach a generic greeting, or the person answering has no clear knowledge of the candidate's supposed employment history.
Real Victim Report
An HR manager in Nashville, Tennessee reported to the FTC that she hired what appeared to be a senior software developer through her company's online application portal. The candidate's resume listed ten years at reputable tech firms, had a professional LinkedIn profile with hundreds of connections, and interviewed exceptionally well via video. Within two days of being added to the payroll system, the employee was marked as a no-show. When the HR manager tried to contact them, the phone number was disconnected and the email bounced back. She later discovered that during the brief time the fake employee was in the system, someone accessed the company's employee database, exposed personal information for 247 staff members, and attempted to change banking details for direct deposits. The incident cost the company over 85,000 dollars in incident response, forensic investigation, and employee credit monitoring services.
What To Do If You've Been Targeted
Immediately stop all communication with the candidate and remove them from any company systems, email, or access portals. If they are already hired, lock them out of systems right away and notify your IT department.
Preserve all evidence of the suspicious application, emails, messages, and interview records. Take screenshots of their LinkedIn profile, resume, and any documents they submitted before they disappear or are deleted.
Report the fraud to the FBI's Internet Crime Complaint Center at ic3.gov. Include the applicant's name, email address, phone number, IP address (if you have access), and detailed description of what occurred. The IC3 combines reports to identify criminal networks.
File a complaint with the Federal Trade Commission at reportfraud.ftc.gov. The FTC aggregates job recruitment fraud reports to track patterns and warn other employers and job seekers.
Notify your company's legal and security teams immediately. Conduct a full audit of company systems to determine if any data was accessed or stolen. Check payroll records, employee databases, and client information systems for unauthorized access.
If money was sent or company banking information was shared, contact your bank and financial institutions immediately to freeze accounts, block unauthorized transfers, and add fraud alerts to your business accounts.
Implement a company-wide fraud alert to all HR and hiring managers about the incident, share the candidate's details (name, email, phone, photo), and establish new verification protocols for all future applicants.
How To Protect Yourself Going Forward
Verify every candidate's claimed employment history by calling the main company phone line and asking to be transferred to the HR department, not by using contact information provided by the candidate. Ask for specific details about their role, tenure, and manager names that can be independently verified. Use background check companies that specialize in employment verification and have relationships with major employers to confirm work history without relying on applicant-provided references.
Implement a two-factor authentication system for all new hires before adding them to payroll, and require government-issued photo ID verification via video call or in-person. Slow down your hiring process intentionally, even if you're desperate to fill positions. Most scammers move quickly and get impatient when interviews or onboarding takes weeks rather than days. Schedule final interviews with multiple team members and ask questions that require detailed knowledge of the industry, your company's specific operations, or technical skills that cannot be faked.
For remote positions, require a video interview that includes recording the candidate's government ID and having them show identification live on camera. Use LinkedIn's verification tools and cross-check candidate profiles against public records, previous employers, and university alumni databases. If any detail feels off, run a reverse image search on their LinkedIn photo to see if it appears elsewhere online or matches other suspicious profiles. Do not add anyone to payroll, create email accounts, or grant system access until their background check is fully completed and they have passed all verification steps in person or via trusted third-party services.